My80211.Com OTAP Article Picked Up By Computerweekly.Com
 Saturday, November 7, 2009 at 9:41AM
Saturday, November 7, 2009 at 9:41AM Computerweekly.com picked up my article "There is more to the recent Cisco Wireless OTAP issue that isn’t being widely reported." about the controller information being sent in the clear when OTAP is disabled.
Read more about it here:
Cisco wireless routers may still be vulnerable to remote attacks even if remote management is disabled, a wireless engineer has warned.
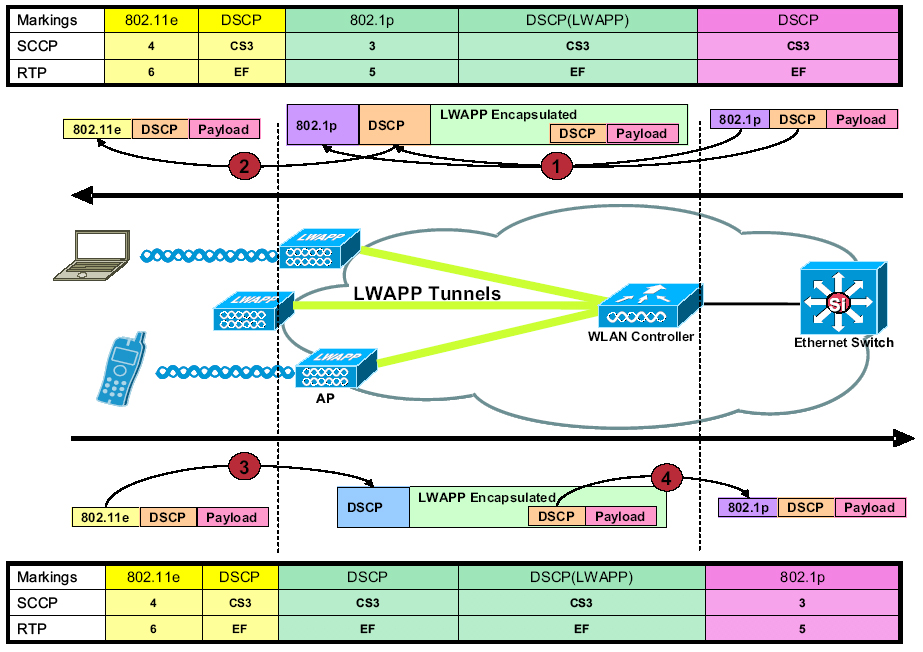
As Computer Weekly previously reported, Cisco access points have a potential vulnerability in the Over the Air Provisioning (OTAP) feature.
This function allows a Cisco access point that is not connected to a Cisco controller to listen to traffic from other nearby Cisco access points and to use that information to quickly locate and connect to a nearby wireless Lan controller. However, AirMagnet, a supplier of network sniffing tools, has warned that a rogue access point could use the OTAP feature to connect to a corporate network.
Cisco recommends disabling OTAP after a wireless access point has been deployed, but wireless engineer George Stefanick has posted a video in which he claims Cisco access points can be attacked, even when OTAP is disabled. "If you run a corporate network, you do not want to broadcast any more information that you have to, especially if [the network] is wireless. Even if OTAP is disabled, information is still being broadcast."
In particular, information about the network address of the wireless controller and the IP address of the management console are broadcast, irrespective of whether OTAP is enabled, he said.
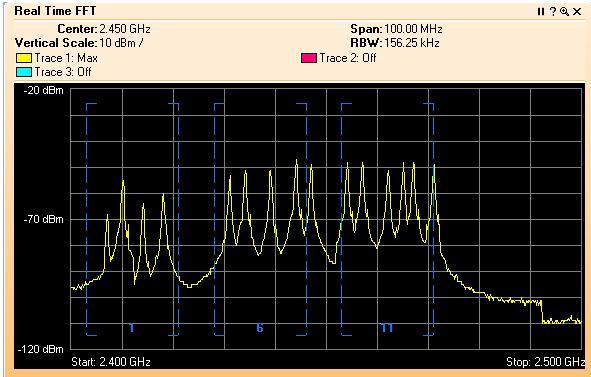
Stefanick said that since the OTAP protocol runs at low bandwidth, it can travel long distances, as much as 100ft, allowing a hacker to find information about the corporate network. Such information could be used to attack the network.
Cisco recommended using DHCP or DNS as the preferred way to configure wireless access points. Disabling OTAP is purely a best practice to eliminate unused features, Cisco said.
 George |
George |  Post a Comment |
Post a Comment | 




Reader Comments