7/27/09 - Cisco Security Advisory: Multiple Vulnerabilities in Cisco Wireless LAN Controllers
 Tuesday, July 28, 2009 at 7:38PM
Tuesday, July 28, 2009 at 7:38PM Summary
Multiple vulnerabilities exist in the Cisco Wireless LAN Controller (WLC) platforms. This security advisory outlines the details of the following vulnerabilities:
- Malformed HTTP or HTTPS authentication response denial of service vulnerability
- SSH connections denial of service vulnerability
- Crafted HTTP or HTTPS request denial of service vulnerability
- Crafted HTTP or HTTPS request unauthorized configuration modification vulnerability
Cisco has released free software updates that address these vulnerabilities.
This advisory is posted at: http://www.cisco.com/warp/public/707/cisco-sa-20090727-wlc.shtml
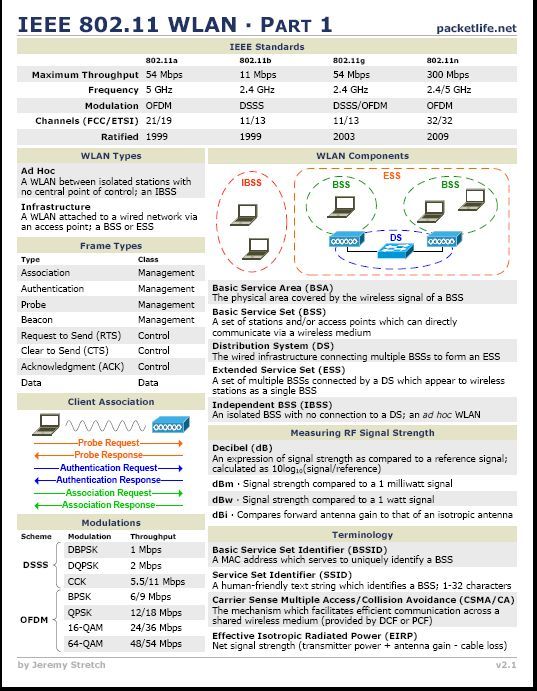
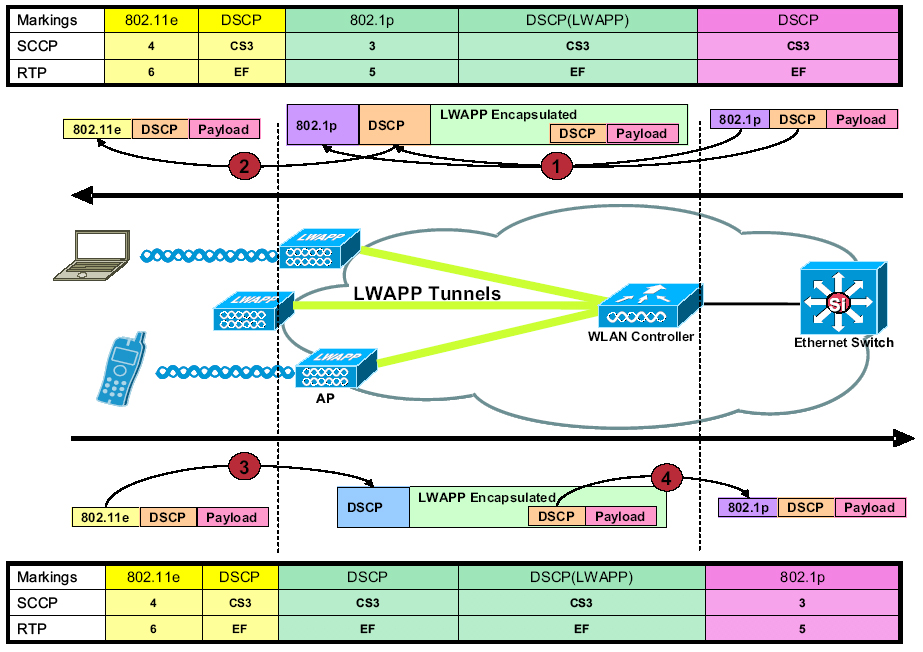
Cisco Wireless LAN Controllers (WLCs) are responsible for system-wide wireless LAN functions, such as security policies, intrusion prevention, RF management, quality of service (QoS), and mobility.
These devices communicate with controller-based access points over any Layer 2 (Ethernet) or Layer 3 (IP) infrastructure using the Lightweight Access Point Protocol (LWAPP).
This security advisory describes multiple distinct vulnerabilities in the WLC family of devices.
- Malformed HTTP or HTTPS authentication response denial of service vulnerability
An attacker with access to the administrative web interface via HTTP or HTTPS may cause the device to reload by providing a malformed response to an authentication request.
Note: The vulnerability can be exploited only via the administrative web-based interface; Web Authentication features are not affected.
This vulnerability is documented in Cisco Bug ID CSCsx03715 ( registered customers only) and has been assigned Common Vulnerabilities and Exposures (CVE) ID CVE-2009-1164.
- SSH connections denial of service vulnerability
Affected devices may be susceptible to a memory leak when they handle SSH management connections. An attacker could use this behavior to cause an affected device to crash and reload.
Note: A three-way handshake is not required to exploit this vulnerability.
This vulnerability is documented in Cisco Bug ID CSCsw40789 ( registered customers only) and has been assigned CVE ID CVE-2009-1165.
- Crafted HTTP or HTTPS request denial of service vulnerability
An attacker with the ability to send a malicious HTTP request to an affected WLC could cause the device to crash and reload.
Note: The vulnerability can be exploited only via the administrative web-based interface; Web Authentication features are not affected.
This vulnerability is documented in Cisco Bug ID CSCsy27708 ( registered customers only) and has been assigned CVE ID CVE-2009-1166.
- Crafted HTTP or HTTPS request unauthorized configuration modification vulnerability
An unauthorized configuration modification vulnerability exists in all software versions prior to the first fixed release. A remote, unauthenticated attacker who can submit HTTP or HTTPS requests to the WLC directly could gain full control of the affected device.
Note: The vulnerability can be exploited only by submitting such a request to an IP address that is bound to an administrative interface or VLAN.
The vulnerability is documented by Cisco Bug ID CSCsy44672 ( registered customers only) and has been assigned CVE ID CVE-2009-1167.
You can read more at: http://www.cisco.com/en/US/products/products_security_advisory09186a0080adb3d7.shtml#@ID
 George |
George |  Post a Comment |
Post a Comment | 





Reader Comments